Venus Exploit Post-Mortem: How to Profit in a Flash Loan Window?
Original Article Title: "Retrospect of How I Profited from the Venus THE Attack"
Original Article Author: Weilin (William) Li, Crypto Trader
Editor's Note: Last night, the BNB Chain's leading lending protocol, Venus Protocol, was attacked, with abnormal activity in THE liquidity pool. THE experienced a short-lived spike of 116% to $0.6, followed by a rapid drop of over 60%. The Venus Protocol team responded, stating: "We are actively investigating the abnormal activity in THE liquidity pool, and to prevent further abuse, we have taken precautionary measures: immediately suspending all borrowing and withdrawal operations for THE. Other markets remain unaffected and will continue to operate as normal."
Amidst THE's sharp price swings, many traders seized the brief opportunity window to profit. This article, from crypto trader Weilin (William) Li, recounts the Venus Protocol attack and the profits made. The original content is as follows:
Two hours ago, VenuV's THE suffered a very typical Mango Markets-style price manipulation attack.
The attacker targeted the low liquidity collateral asset THE:
· Initially collateralize THE
· Borrow other assets
· Further buy THE with borrowed assets
· Continuously push THE price up
· Upon average oracle update, obtain higher collateral value, then continue the borrowing loop.
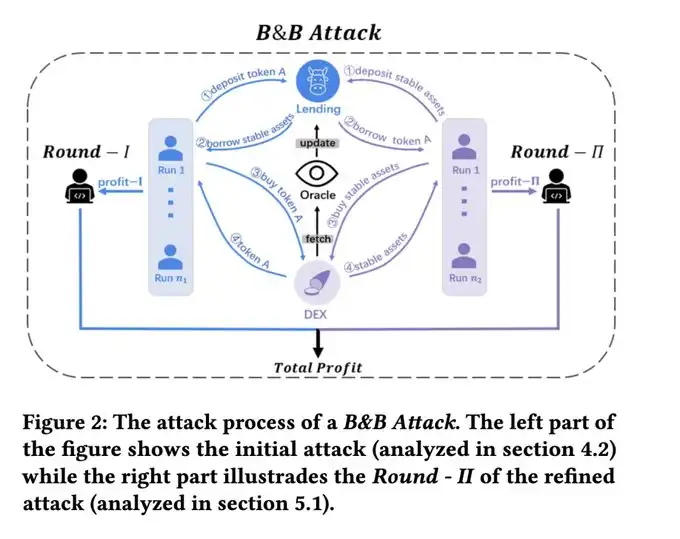
From my paper: Unmasking Role-Play Attack Strategies in Exploiting Decentralized Finance (DeFi) Systems (https://dl.acm.org/doi/10.1145/3605768.3623545)
Due to THE on-chain illiquidity, the price was brutally dragged from $0.27 to nearly $5. The oracle price was then updated to 0.5 (time-weighted average), allowing the attacker to further leverage up.
More crucially, THE itself has a supply cap.
Normally, this would restrict the attacker from further expanding their position. But they used a classic trick to bypass this: the Compound fork's donation attack. After depositing a large amount of THE, directly transferring THE to the vTHE contract, they continued raising the recognized collateral value through a "donation" to further surpass the cap.
Attack Transaction: 0x4f477e941c12bbf32a58dc12db7bb0cb4d31d41ff25b2457e6af3c15d7f5663f

Attack Transaction: 0x4f477e941c12bbf32a58dc12db7bb0cb4d31d41ff25b2457e6af3c15d7f5663f. Expanding collateral through donation
After the first wave of attacks, THE price roughly stabilized around $0.5.
By this point, the attacker could have already walked away with the borrowed assets. However, they evidently wanted to maximize profits and continued to pour the borrowed assets into buying THE, attempting another round of surge.
But here's the issue: While the price was exceptionally high, the market selling pressure also became extremely exaggerated. The attacker kept buying but could hardly move the price further. Eventually, he nearly depleted his own collateral capacity, with a health factor close to 1, on the brink of liquidation.

THE Price Movement
At this point, the situation became very clear: The collateral in the attacker's possession, including their pre-allocated assets and the THE purchased during the attack, had a nominal value of approximately 30M. However, the core issue with this collateral was — there was simply not enough liquidity to absorb it. Once the liquidation began, this THE could only be aggressively dumped on the market. Yet in the market, no one would be willing to buy such a large amount at that inflated price.
So what did I do?
At the start of the liquidation, I directly opened a short position on THE. And this position could actually have a relatively higher leverage.
The reason is very simple: overvaluation, low liquidity, massive passive selling pressure, no buyers.
The result was not surprising either: after the liquidation, THE price plummeted to around $0.24, even lower than the price before the attack, as the original holder also sold during the process.
Here, I closed the short position, making a profit of about 15K.

My Short Position
In the end, Venus was left with around 2M bad debt.
As for how much the attacker actually made, I have not completed a full calculation yet; but from the operations of some of the addresses, he most likely barely made any money, and may have even wrecked himself. However, the attacker may still have off-exchange perpetual positions to make money (just like our operation).
Venus's around 2M bad debt address: https://debank.com/profile/0x1a35bd28efd46cfc46c2136f878777d69ae16231
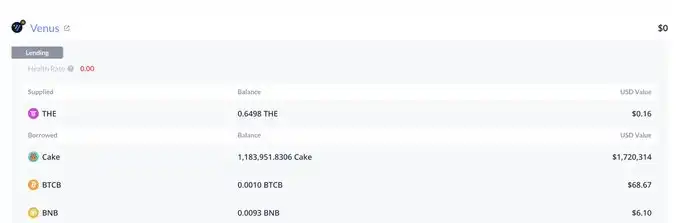
Venus's ~2M Bad Debt:
https://debank.com/profile/0x1a35bd28efd46cfc46c2136f878777d69ae16231
This incident once again illustrates:
In DeFi, “Nominal Collateral Value” does not equal “Liquidation Value.” When the collateral itself lacks liquidity, the system may see 30M, but what the market can truly realize may be close to zero.
I published a paper in my 23rd year, titled Unmasking Role-Play Attack Strategies in Exploiting Decentralized Finance (DeFi) Systems, where I provided a detailed mathematical model of this attack. Interested readers can refer to: https://dl.acm.org/doi/10.1145/3605768.3623545
You may also like

The biggest DeFi heist of 2026, hackers easily took advantage of Aave

Will Robots Replace Humans? He Says No!

Binance Coin's Price Skyrockets 15x to All-Time High, Saved by Three Bull Market Lifelines

The organization has accessed the prediction market, but is stuck at the third stage

Head of crypto VC collective shrinks: a16z crypto fund management scale plummets by 40%, Multicoin cut in half

Arthur Hayes New Post: It's "No Trade" Time Now

Claude Opus 4.7 Review: Is It Worthy of the Title of Strongest Model?

DWF In-Depth Report: AI Outperforms Humans in Yield Farming Optimization in DeFi, But Complex Transactions Still Lag Behind 5x

The financial tricks of the crypto giant Kraken

When proactive market makers start to take initiative

Massive Whale Movement: Unstaking $84.96 Million in HYPE Tokens
Key Takeaways A crypto whale, known as TechnoRevenant, has unstaked approximately $84.96 million in HYPE tokens. The tokens…

ListaDAO Addresses Third-Party Contract Vulnerability Concerns
Key Takeaways GoPlus Security revealed a vulnerability in a contract resembling those of ListaDAO. ListaDAO confirmed that their…

Security Risks of Fake Ledger Nano S+ Devices Emerging Through Chinese E-Commerce
Key Takeaways Counterfeit Ledger Nano S+ devices are being sold on Chinese e-commerce platforms, posing significant risks to…

Wave of Cyber Attacks Hits DeFi Protocols Post-Drift Hack
Key Takeaways A significant $280 million attack on Drift Protocol set off a chain of security breaches across…

Tom Lee Says ‘Mini Crypto Winter’ Is Over, Sees Ether Above $60K
Key Takeaways: Tom Lee predicts Ether’s resurgence, projecting it to surpass $60,000 in the coming years. Bitmine suffered…

French Government Tackles Rising Crypto Safety Concerns
Key Takeaways: France is intensifying measures to counter the surge in crypto kidnappings and wrench attacks. Since early…

Europe’s Bitcoin Treasury Playbook Unlikely to Mirror US Strategy: PBW 2026
Key Takeaways: European firms are adapting unique Bitcoin treasury strategies due to distinct financial regulations and market dynamics…

Circle Confronts Lawsuit Over $280M Drift Protocol Hack
Key Takeaways: Circle faces a lawsuit for allegedly aiding in the transfer of $230 million in stolen USDC.…


